By mitigating Onboarding Fraud, BFSIs can build customer trust and enhance digital banking security. It helps to deter fraudulent account creation, identity theft, and financial fraud, making the onboarding process safer for legitimate customers.
Onboarding fraud minimization also helps BFSIs avoid financial loss and ensure compliance with KYC and AML laws. Advanced fraud detection technologies enable banks and financial institutions to detect suspicious activities in time and stop the activation of high-risk accounts.
Onboarding fraud prevention optimizes operations by minimizing manual verification processes and fraud investigations. It also helps BFSIs to provide quick, secure, and effortless customer onboarding while ensuring brand reputation and long-term success.
The Impact of Reducing Onboarding Fraud on BFSIs
Introduction
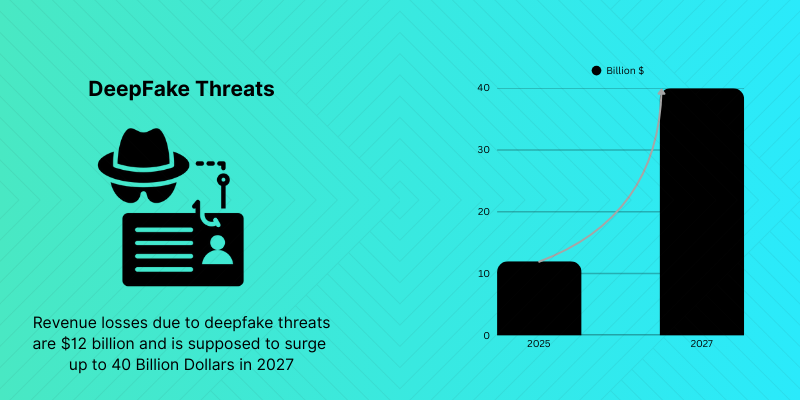
The Banking, Financial Services and Insurance (BFSI) industry is quickly moving towards digital transformation, presenting a more streamlined and convenient customer onboarding experience. But this digital transformation has also made them more vulnerable to advanced fraud schemes. Fraud attacks in financial services rise 63%; losses jump 64%
BFSIs are facing a growing issue of onboarding fraud, where fraudsters are exploiting fake identities, synthetic data, stolen credentials, and forged documents to access financial services without authorization.
Protecting customer trust, staying compliant with regulations, and avoiding financial losses can only be achieved if BFSIs take steps to reduce onboarding fraud. With the expanding trend of digital banking and remote onboarding, financial institutions are faced with the challenge of securing their onboarding processes and providing safe customer experience with advanced fraud prevention methods.
Understanding Onboarding Fraud in BFSIs
Onboarding Fraud in BFSIs is when fraudsters register and verify fake identities during the registration and verification process. Some of these fraud schemes include identity theft, synthetic identities, document fraud, and mule account creation.
As the banking sector goes digital, banks are faced with threats from criminals exploiting vulnerabilities in onboarding systems, especially digital lending and mobile financial services. Monzo was fined £21 million after failures in onboarding and risk assessment controls allowed over 34,000 high-risk customers to open accounts. In the absence of robust fraud prevention measures, BFSIs can onboard high-risk individuals who may go on to commit account takeover (ATO) attacks, fraudulent transactions, and money laundering.
Why Onboarding Fraud is a Major Concern for BFSIs
BFSIs deal with highly sensitive financial and customer information and are a perfect target for fraudsters. But the types of fraudulent onboarding can result in:
- Loss of finances due to fake accounts and fraudulent transactions.
- Penalties for non-compliance with KYC and AML requirements by regulators
- Loss of reputation and loss of customer trust. Damage to reputation and loss of customer trust.
- More time and money spent on fraud investigations and remediation. More time and money spent on fraud investigations and remediation.
- Money laundering risks and financial crimes risks
With evolving fraud patterns, BFSIs need to take proactive measures in strengthening the onboarding security to reduce the risk and keep their customers confident.
The Impact of Reducing Onboarding Fraud on BFSIs
Improved Customer Trust
Proper onboarding procedures help customers feel at ease that their personal and financial information is safe. By minimizing Onboarding Fraud, BFSIs can foster better customer relationships and enhance their long-term retention efforts.
Reduced Financial Losses
Unauthorized transactions, loan fraud, chargebacks and money laundering risks can be caused by fraudulent accounts. These monetary risks to BFSIs can be greatly mitigated through effective fraud prevention.
Stronger Regulatory Compliance
BFSIs have to adhere to stringent KYC and AML rules. By minimizing Onboarding Fraud, institutions can stay compliant and prevent legal issues and regulatory penalties.
Faster Digital Onboarding
BFSIs can leverage advanced fraud detection technologies to automate customer verification without compromising on security. This helps to optimize a user’s onboarding experience without delay.
Enhanced Brand Reputation
When financial institutions get hacked or someone is fraudulently added to the payroll list, their reputation can be compromised. Overall, BFSIs are seen as reliable, trustworthy, and dedicated to protecting their customers by taking proactive measures to prevent fraud.
Better Operational Efficiency
Automated fraud detection and identity verification alleviates the burden of compliance and fraud investigation staff. This enhances the operational efficiency and reduces the manual verification expenses.
Key Features of Effective Onboarding Fraud Prevention for BFSIs
AI-Powered Fraud Detection
AI continuously evaluates customer activity and transaction trends, and flags suspicious new user activity as it happens.
Identity Verification Solutions
The advanced identity verification suite validates government-issued IDs, biometrics and customer information to thwart identity fraud.
Behavioral Analytics
Behavioral monitoring allows detecting malicious user activity, bot attacks, and suspicious onboarding behavior.
Device and IP Intelligence
High risk devices and suspicious login locations are detected by device fingerprinting and IP analysis, respectively, and both are flagged as potential points of risk in fraud attempts.
Real-Time Risk Monitoring
BFSIs can use continuous monitoring to identify and prevent fraudulent onboarding before the approval.
AML and KYC Compliance Integration
Integrated compliance checks support compliance and mitigate risks at BFSIs during the onboarding process.
Multi-Factor Authentication
An extra layer of authentication like OTP verification and biometric checks enhances onboarding security.
Conclusion
The impact of reducing Onboarding Fraud on BFSIs goes beyond fraud prevention alone. It strengthens customer trust, enhances regulatory compliance, reduces financial risks, and improves operational efficiency. As digital financial services continue to expand, BFSIs must adopt advanced fraud prevention technologies to stay ahead of evolving threats.
By investing in secure onboarding solutions from industry innovators like Atna AI , BFSIs can deliver seamless customer experiences while protecting their platforms, reputation, and long-term growth in an increasingly digital financial ecosystem.
FAQs
What is Onboarding Fraud in BFSIs?
Onboarding Fraud in BFSIs refers to fraudulent activities during customer registration using fake, stolen, or synthetic identities to gain unauthorized access to financial services.
Why is reducing Onboarding Fraud important for BFSIs?
Reducing Onboarding Fraud helps BFSIs prevent financial losses, maintain regulatory compliance, protect customer data, and improve customer trust.
How do BFSIs detect Onboarding Fraud?
BFSIs use AI-powered fraud detection, identity verification, behavioral analytics, device intelligence, and real-time monitoring to identify suspicious onboarding activities.
What are the risks of Onboarding Fraud for BFSIs?
Onboarding Fraud can lead to financial losses, reputational damage, regulatory penalties, money laundering risks, and operational inefficiencies.
How does AI help BFSIs reduce Onboarding Fraud?
AI helps BFSIs analyze user behavior, identity patterns, and risk indicators in real time to accurately detect and prevent fraudulent onboarding attempts.